A Guest Post by Cosmopolitan Scum

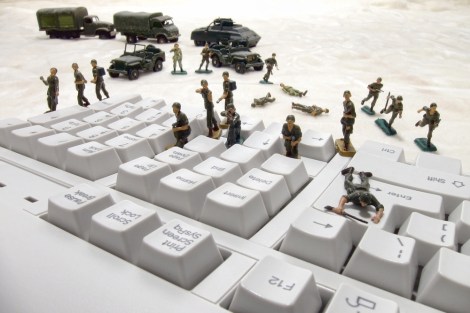
Military and intelligence stories have been all over the news recently. Be it indiscriminate eavesdropping programs, WMD infrastructure, or our impending doom at the hands of terrorists if we vote “yes”, there is a common denominator in the statements of the high heid yins: these are issue for the big boys, the role set out for the rest of us is to cower in fear and not to hurt our wee brains trying to understand. In the independence debate, we are warned that an independent Scotland is going to be overrun by terrorists, disastrously cyber-attacked, or run out of money trying to prevent these disasters from happening. The catalyst of the recent wave of scare stories is a report by a bunch of military and intelligence insiders, the crowd treated in the mainstream media as holding an exclusive grasp of the serious issue of our national security. But this deference is exactly the type of elitist approach that led us into the intelligence SNAFU we are in at the moment – with the agencies at odds with the democratic process and public control. The independence debate is a chance for us to crack open the debate on intelligence and the military, and imagine what a security apparatus actually subservient to democracy might look like.
The report from the Scotland Institute, “Defence and Security in an Independent Scotland”, that dropped last month is the perfect opportunity to open these issues to wider discussion. It is also a prime example of the problems in current elitist and alienating security discourse. Upon its release the report was promoted by one of it’s authors, retired Major General Andrew Mackay. Mackay is an officer whose resignation from the British Army in 2009 caused quite a stooshie due to the pelters he gave the MOD: according to the General, despite a decade of counterinsurgency hype in Iraq and Afghanistan, London’s messages had “no relevance at ground level”, the Army “consistently failed” to understand Afghan “hearts and minds”, careers in the military were built on “budgetary and management incompetence”, and the structures at the MOD are “institutionally incapable” of adapting to contemporary conflict (a point of view which rather undermines Better Together’s Facebook PR for the report – “We think the UK Armed Forces are the best in the World: Like if You Agree”). A break from this military dinosaur, staggering wildly through the world of contemporary geopolitics blindly prodding at hornets nests of human misery and insecurity, Mackay argues, would be too much of “a risk to our security” to choose independence. Better stick with the old ways and the trusted pair of hands than go it alone into the scary, insecure world.
The paper deals with both military and intelligence policy. In the first case – despite a doom-mongering executive summary and PR drive – the report basically concedes that we can afford to protect ourselves, though not to maintain the status quo of military spending and activity. Fortunately, most of the arguments the War Men put forward for keeping the union and the MoD are more effective when repeated unedited as arguments for independence. “We Scots are indeed a warrior race”, Mackay writes, and have “always provided a disproportionate number of soldiers to the UK armed forces”. For centuries, that is, Scottish men and women have been patronized and exploited as a tribe most fit to go and die in the Queen and the Tory’s wars, and indeed have gone and done just that in disproportionate numbers. An independent Scotland will mean, the report warns, that Scottish soldiers will have to “forge new identities” outside of the British military – without the familiar referents of the loyal hardman ‘Jock’, the jokes about smack and poverty, a “Royal Regiment” topped up with foreign soldiers due to a recruitment crisis, and an officer class stacked with English public schoolboys. A fresh start, with respect to the history, is hardly the nightmare scenario.
On an independent military force, the report basically boils it down to a debate about how effective and moral you think violence is as a primary mode of engaging with other nations is. If you yearn for the days of the glorious military stoating about invading everyone, I’m afraid the options don’t look too good for you an independent Scotland. The report doesn’t say we couldn’t afford a military to defend us. In fact, it says we would “in some limited form, be able to provide for [our] defence”, through a defence force which “does not really need much more than an effective coast guard, a reliable police force and good intelligence service to secure its citizens”, a capacity which would come “reasonably cheap”. Any expeditionary capacity would be limited to “peacekeeping duties perhaps or the provision of smaller units in specialist roles”. Sounds like a thoroughly reasonable starting point for planning the armed forces of a new country to me.
So, the report acknowledges that whilst we wont be able to fight for The Empire, we’ll probably manage awrite in regards to the military. Many of the scary headlines, however, followed from its conclusions in other areas. The military or security threats faced by a nation like Scotland are – the paper argues – not the “existential threats of invasion or subjugation”, but of terrorism, organised crime, and cyberwarfare. It is in these areas, of intelligence and cyberspace, that we will really miss r-UK capabilities and suffer – the paper argues – increased insecurity. The arguments here are both more serious – we can change our military strategy and thus military commitments, but we can’t have such an effect on the threats from outside which are unpredictable and uncontrollable.
The Spectre of Terrorism
 Of course, that outside threats are uncontrollable is a huge fallacy. The link between threats to national security – from political instability to terrorist attacks – and foreign policy are almost universally recognized outside of the public statements of warmongering politicians. In terms of counter-terrorism, the implication of the “no” security argument is that an independent Scotland would be highly vulnerable to the Al Qaeda boogie man who is just biding his time, waiting for us to naively throw off the protective umbrella of Great Britain so it can detonate a dirty bomb on Sauchiehall Street or behead Bernard Ponsonby on YouTube.
Of course, that outside threats are uncontrollable is a huge fallacy. The link between threats to national security – from political instability to terrorist attacks – and foreign policy are almost universally recognized outside of the public statements of warmongering politicians. In terms of counter-terrorism, the implication of the “no” security argument is that an independent Scotland would be highly vulnerable to the Al Qaeda boogie man who is just biding his time, waiting for us to naively throw off the protective umbrella of Great Britain so it can detonate a dirty bomb on Sauchiehall Street or behead Bernard Ponsonby on YouTube.
This notion of the latent threat of Islamist terrorism however, neglects they key point that in disassociating ourselves from (though never forgetting) the crimes and horrors of more than a decade of the ‘War on Terror’ and moving to a foreign policy based on dialogue and cooperation rather than racist exceptionalism and habitual strategic miscalculation, we remove one of the key drivers for such attacks. This is the truth that is usually treated by politicians and the media as anywhere between starry-eyed hippy bullshit and capitulation to ‘the terrorists’ – but is openly acknowledged by terrorists themselves (see both Osama Bin Laden and Mohammad Sidique Khan) and our existing intelligence agencies. Terrorism of they type we are warned about is largely ‘propaganda of the deed’, in this case it is difficult to imagine even the most deranged plotter judging an attack on a nation which has made the choice to extricate itself from the “coalition of the willing”, weakening one of the key members in the process, to be good strategy.
This isn’t to say we will live in a threat-free world. I’d like to live a right-on world where there was no need for intelligence agencies – I hope that’s what Scotland is like. But we wont be able to change what the world is like – some crazy people might still want to attack us to make some political point, other countries will still seek clandestine means of influence, and some groups might seek to subvert political life outside of the norms of our new politics. So, we’ll need an intelligence capacity to deal with counter-terrorism, counter-espionage, and to protect the political process. The current defence capacity in these cases comes from the UK security services (MI5, 6 and GCHQ), and the Scotland Institute paper warns of the potentially huge cost and complication of setting up an independent equivalent. The chance of the UK breaking off a bit of these organisations for us – or even just geeing us some staff – is zero for political and security reasons. But would we want it anyway? A Scottish security service will have to build up facilities and a cadre of staff from scratch, so what might we want it to actually do?
Rather bizarrely, some unionists have held up the Glasgow airport bombings as an example of why we need the London security apparatus. This overlooks two somewhat important points: firstly, the attack would likely not have happened had Scotland been an independent country uninvolved in America’s decade long revenge fantasy in Afghanistan and Iraq; and secondly, THE ATTACKS FUCKIN HAPPENED, yer mighty and indispensible intelligence agencies failed and only the attackers ineptitude and Smeato saved us. Still, we would be negligent to assume that we will be 100% immune to the whims of crazy people who want to use violence to further their cause. Such attacks would most likely be aimed at the soft spots of a modern democratic nation – key infrastructure (oil, nuclear, transport) or mass-casualty attacks on key population centres. How can these be defended against in a proportionate way?
The first step, is for the military and policing capacity to be developed to cover these extremely unlikely contingencies. A refocused military – based on actual defence, as the report suggests – could specialise in maritime security and infrastructure protection. This would seem the obvious focus not just from a national security perspective, but also a military one as climate change and resource wars lead to the militarisation of the sea to our north. This role should also recognise that securing the sea from pollution and overfishing, and our transport infrastructure from disruption (e.g. extremes in weather) are vital to our national interests; meaning our soldiers get the chance to gain operational experience, work with communities, and perform socially necessary tasks – not just gobble cash sailing about in useless, anachronistic, Armageddon machines and paranoically plan for the big one.
Similarly, the police should play a security role in relation to keeping population centres safe (you know, their job) – an area in which they have plenty of experience after decades of policing the periphery of the Troubles. To do this, there must be accountability and trust, and a reckoning with the problems of the past must be a key component in building a more democratic and open police force for the future. Despite a decade of mass surveillance, ‘big data‘ TED talks, and all seeing “Death Stars” touted as the must have military intelligence asset, it should be recognized that the most effective form of intelligence against terrorist attacks in a small nation is human intelligence – from working with informants and through broader community engagement initiatives. Consequently, good relations between the police and local communities must be seen as a key element in national security. Instead of militarising the police, this should give the impetus for a more transparent and accountable police force – not a sneakier one – whose alienation of any community should be seen as a complete dereliction of duty and lead to responsive and open reform.
In recognition of the central role a re-focused military and police can play in national security – one of the key jobs of any intelligence agency will be one of coordination, rather than rivalry or parallel activity. This coordination should not be done in a clandestine way – the arrogance of the UK government’s matter-of-fact “we don’t discuss intelligence matters” must go. The work of the military and police should not, with very few exceptions, be secret, so the working of most of the pieces of the intelligence apparatus should already be open to public scrutiny. Oversight of the intelligence service should be as transparent as possible – radical transparency should be the bulwark against abuses of power, as well as inefficiency and bad policy. Where details cannot be published for operational or tactical reasons, an elected group of overseers should have access to this material, this body should also deal with Freedom of Information requests into material which is not made public – allowing classification to be challenged and justified in a transparent way outside of security institutions themselves. These sort of structures would produce an accountable and proportional response to terrorist threats – which bring the organisations of the state together with communities in a useful way, rather than allowing the specter of terrorism to drive us apart.
Securing the political system
Beyond such measures, however, the state will also need a small operational capacity to deal with issue of counterintelligence, in recognition of the fact that other countries intelligence agencies will seek opportunities to influence the political, military and industrial elements of a new state. This operational capacity need not be very large. Finland (with a similar population to Scotland), for example, has an intelligence agency of 220 policemenwith additional training. It costs them €7-8m per year and focuses on counterterrorism, counterintelligence, and security bureaucracy (providing security clearances, protecting VIPs, etc.). The Finnish agency has a 70-80% confidence level of population, it also publishes annual reports into its activities.
Fighting of the spies of the world might seem like a big job for a small agency – but we’re not talking about protecting nukes from the Russians (there will be no nukes), running proxy wars or plotting to overthrow democratically elected governments abroad. We’re largely talking about the protection of the intellectual property of Scottish organisations, and maintaining the integrity of the political system (e.g. making sure MI6/CIA/Chinese MSS aren’t blackmailing politicians). In the case of industrial and organizational secrets, protection generally takes the form of providing information, advice, and training on best practice: there is not a serious competitive company which does not independently protect its own secrets and assets, the state can simply provide an extra level of coordination. An investigative capacity into serious breaches could be maintained (through the secondment of experts from industry or academia) as an option of last resort, which can feed into developments of best practice through ‘lessons learned’.
As for maintaining the integrity of the political system – probably the essential task in securing a new state like Scotland – we should begin by realising that much of work must be done in the design of that system itself. The easiest way to protect the integrity of a political system is transparency – meaning that outside interference or internal corruption is caught early and publicly. In this respect the world of political influence – from lobbying by corporate or foreign interests, to outright bribery – forms the primary threat to the independence and integrity of political representatives, and thus the system. Lobbying should be heavily regulated and publicly scrutinised – as well as ensuring compliance with regulation, the intelligence agency could take the lead in investigating breaches of transparency (illegal lobbying practices, failures of disclosure, etc.), the results of which should be published, forcing both politicians and potential influencers into compliance, and allowing critical public engagement with this insidious area of extra-parliamentary politics.
The best way to avoid outside influence on government in a small, new country with a proportionate counter-intelligence capacity is radical freedom of information. If we are worried about outsiders influencing and corrupting the political process, there is an obvious way to guard against this. All politicians and civil servants communication should be published – along with all other business of government – as standard. This will provide important public insight into the workings of government at a vital time in the formation of a new country, it will allow us to hold politicians accountable for their public statements, and will provide a bulwark against outside influence. In this situation, the role of the intelligence agency would be to police the margins of transparency: investigate attempts to circumvent FOI norms, facilitate whistle-blowers to fix problems in the system, and become the first port of call for any official facing any form of pressure from outside interests. As this would be done – by design – in the open, the intelligence service would be working transparently to protect the political process, not as the intelligence arm of any government or political faction.
Life after GCHQ
The other key area of the security apparatus discussed in the Scotland Institute study – one which has been discussed elsewhere by Andrew Neal and at Foreign Affairs Committee on post-Indy intelligence – is GCHQ – the perverts that have been in the news recently for spying on the entire internet. The argument goes that Scotland would need a “mini-GCHQ” to provide the same capacity on a smaller scale. The approach of the NSA and GCHQ is to collect everything they can usefully analyse on everyone they can get away with targeting. The work of the organisations is conducted in almost total secrecy, with minimal effective oversight, and extremely limited accountability. It is based on a worldview of constantly evolving threats – on the paranoia of stopping the next ‘black swan’ event like 9/11. These institutions are the result of imperialist neuroses – desperately trying to fight the symptoms of the War on Terror, whilst looking on in horror as the effects of technological globalisation swamp them with data they desperately need to make mean something.
The US national security state spends hundreds of billions annually on cybersecurity and eavesdropping – it needs nearly 5 million people with security clearances to run it – the entire population of Scotland. GCHQ’s budget runs to £100s of millions annually, and the “mini GCHQ” discussed in the Scotland Institute report would apparently cost £1.5b to start up and £200m annually. The first question here is: what exactly is a “mini GCHQ”? – how does one miniaturise an endeavour to monitor the entire internet? Perhaps we’ll only tap the fibre optic cables that make landfall in Scotland? Maybe we’ll only coerce Scottish companies into giving us their user information in secret? The report says we would need such a capacity to operate in two areas: signals intelligence collection (eavesdropping) and sharing, and cyberwarfare.
On signals intelligence the warnings are stark – moving outside of the global surveillance umbrella of the “Five Eyes” nations (US, UK, Canada, Australia and New Zealand SIGINT sharing agreement, otherwise known, very catchilly as AUSCANNZUKUS) will leave us “much more vulnerable to terrorist attack”. However, there is no evidence presented that this intelligence partnership has ever stopped an attack on Scotland – on the other hand, we know that the one at Glasgow Airport did happen – right under their Five Noses.
Here’s a suggestion: we don’t need any massively expensive, voyeuristic, panopticon like GCHQ. There is no evidence that this form of large-scale, invasive and secretive surveillance is actually any more effective than more traditional artisanal policing and intelligence techniques in small states. Sure, if your fighting a Global War on Terror it might be handy to monitor the whole globe for SIGNINT on your enemy (and even this is disputed) – but this is not standard practice, its the exception. In any case, reports suggest that very few actual terrorists use online tools that can be easily traced and analysed – Osama Bin Laden wouldn’t use the phone, the US hasn’t been able to find Mullah Omar in 12 years, and everyone knows the way to get killed in a drone strike is to use a mobile or sat phone – there is a massive invasion of privacy for very small intelligence benefit.
Not only could we not afford this type of system, it simply would not fit our needs. The forms of big-data spying they do at the NSA and GCHQ just doesnae work at the level of a population of 5 million people. In recent revelations on the NSA surveillance program, an official said individuals “three hops” away from a target can be marked for further investigation – this means that when a targets contacts are analysed, analysts can then “hop” to investigate the people they contacted, and then “hop” further to target the more distant people that those ones contacted. If we assume everyone has 50 contacts, this means that investigation of just one suspect could lead to a further 127,550 people being marked as targets for more detailed surveillance. The scale of this form of intelligence analysis is not a human one – it is based on algorithms, averages, patterns – and fates can be decided on these. A Scotland of 5-6m people can afford – in both sense of the world – signals intelligence on a human scale, wiretaps based on warrants and strict legal oversight.
In one of the reports more bizarre claims, it says that there would be problems with intelligence sharing with our international spy colleagues if we were to reject GCHQ-style methods. Mackay raises the issue of “our very special relationship with the United States [which is] founded largely on a unique intelligence and defence partnership”, and the report argues that “bluntly put, the US will hardly commit to intelligence sharing with an [independent Scotland] intent on nuclear disarmament”. Cool mate, maybe we’ll just let them use the Hebrides as a torture archipelago, or behead and crucify some criminals, and they’ll let us sit at the big boys table. It seems to me that the US will commit to any arrangement which benefits them, and if that is the Scotland that exists, that is the one they will deal with. We won’t need access to, like, the entire email history of everyone in the world, just a “heads up” if we might be attacked, or someone dodgy turns up here. It is in no one’s interests to let Scotland be attacked out of spite – and to suggest so reeks of desperation. We could also work the way almost every other small country’s intelligence agency works, in cooperation with other nations through international organisations like Europol, EU SatCen, and Interpol. Or we could bankrupt ourselves building a useless, unpopular and abusive spying apparatus so America keeps talking to us, whatevs.
Every time I hear the word “Cyber” I reach for my claymore
The other thing that GCHQ does is cyberdefence. The concept is almost perfectly crafted for the anti-democratic scaremonger – cybersecurity has been roundly hyped as the big issue in military and security in the last few years, discussed almost in complete ignorance of what it means. For example, witness the recent documentary on cyberwar and cybercrime by BBC security correspondent Gordon Corera: every question to anyone is “but isn’t this SCARY?!”; “Britain” was said to be “under attack” when the interviewee really meant some British companies; and the “’Cyber-attack’ threat to London’s Olympic ceremony” was, um…nothing but a false alarm, which the organisers were, in any case, prepared for. Cyber is a great prefix for the War Men and the online security profiteers – it makes everything sound very scary and complicated and inaccessible, and seems like it must be very expensive too. It is a perfect storm of security-elite bullshit.
The report says that “the cyber threat is…one which has the capacity to evolve with almost unimaginable speed and with serious consequences for the nations security” – ooooh scary. Elsewhere the report lists “satellite or communication malfunction” as a threat, which also sounds terrifying until you realise that resilience to this sort of threat was precisely the reason the internet was invented. Other ‘experts‘ have said that we will need a “cryptographic capability and so on if [Scotland] is going to keep its own secrets”, which also sounds fancy but WHAT DOES THAT EVEN MEAN? Effectively unbreakable cryptographic tools are available both on the open market and open source (some even produced by the US military, LOL), good communication practice is all that is required to secure information. The only people this sort of obfuscatory discourse helps are those who want to see more military and intelligence funding and power, and the cyber-security companies themselves.
Not surprising then, this is the sort of discourse that has surrounded ‘cyber’ initiatives coming out of London since day 1 (or should I say ZERO DAY), where secrecy and unaccountability is often cloaked in the rhetoric of complexity or niche expertise. To unpack the reality of ‘cyber’, we can look at what an independent Scotland will supposedly be missing: the report holds up the UK’s Cyber Security Strategy as our great potential loss. This strategy is not a security strategy as such, it is a spending strategy – specifically for the distribution of £650m over 4 years from 2010-2014. This money is to be spend to counter, what the UK National Security Strategy identifies as the “Tier 1 threat” of cyber-attack – which includes everything from ‘hostile’ attacks upon UK cyber space by other states” up to a “debilitating state sponsored attack and thus an act of war”. The threats envisioned thus include everything from hacktivists, to fraudsters, to Die Hard 4-style doomsday scenarios. That’s right folks, £162m per year to fight the multi-faceted, potentially disastrous, constantly-evolving threat of cyber-geddon. By way of comparison: the UK is leaving £2bn pounds worth of equipment, more than 10 times that amount, in Afghanistan when it leaves.
The notion of cyberwarfare suggests legions of hackers countering ever evolving threats and producing more and more evil code to attack each other – which, funnily enough, is pretty much exactly what the commercial cyber-security industry (who have, mysteriously, publicly criticised funding levels of cybersecurity by the UK government) does. Most public online infrastructure (government websites, law enforcement databases, tax authorities, etc.) runs on commercial systems and contracts (like Police Scotland just signed up for)- these companies are both legally accountable for, and well placed to protect these systems using commercial security tools. The notion that government – or even intelligence – runs on some super-secret and extra-awesome computing system that we must spend millions of pounds to figure out how to protect is bullshit.
This is a fact recognised in the spending break down of the UK’s Cyber Security Strategy. Aside from the 50% of the £650m going to GCHQ and the 14% to the MoD – which will be both for the development of an offensive cyber capacity and the updating of aging systems – the focus of the UK government spending is fairly mundane. Much of the money is earmarked for public awareness campaigns about fraudsters, academic funding into cyber threats, providing advice to the private sector on securing their systems, and the development of law enforcement strategies to deal with online crime. Cyber security, in the cold light of day, is basically about keeping up to date with changes online, keeping systems secure using commercial tools, and teaching the auld yins and other noobs how not to get scammed.
But what of the crippling cyber attack that could disable our power systems, poison or water, or shut down our transport networks? This is the cybersecurity boogie man invoked by the Scotland Institute, military futurists, and, ahem, cybersecurity salespeople. The key example here is the Stuxnet virus – produced by the US and Israel to attack specific machine interface systems in one specific part of Iranian nuclear production infrastructure (it did not achieve its goal). So, an example of the use of code in probably the largest clandestine international conflict which is the focus of thousands of agents and billions of pounds – hardly a typical case, and not one worth basing an entire security strategy (and impossible budgetary requirements) on. It should also be noted that there is a large asymmetry in the ability of state hacking – one expert says that “unlike traditional warfare, more resources does not necessarily equate to more power in cyberspace”. The high quality of Scottish computing science education and industry was mentioned in the Foreign Affairs Committee hearing on these issues – supporting this capacity would seem a much better option than bankrupting ourselves to fight a cyber war which an influential expert has said “will not take place“.
The second high profile example of cyberwar is a Russian cyber-attack on Estonia in 2007. As part of a political disagreement the ex-occupier, bullying neighbour and dwindling global power (sound familiar?) engaged in a semi-official attack on Estonian financial and political infrastructure – mainly using DDOS attacks (the same kind Anonymous are known for) to slow down (and sometimes temporarily disable) key systems in Estonia’s highly-networked public services, media, and banking system. I’m no pointing any fingers, but this is perhaps a much more likely scenario. The case of Estonia is perhaps a more appropriate example, then, and guess what: they sorted it out nae bother.
Since 2007 the Estonians have moved an even higher proportion of their government and public services online, with an additional focus on protection of the infrastructure, with the result that now Estonia is one of the best in the world at cyber-defence, frequently held up as the model for other nations (and home to a NATO center of excellence on the subject). Estonia’s military spend – which includes cyber – is €250m and though we don’t have the full figures of the national budget – Estonia’s GDP is less than 1/5 of Scotland’s. Yet it is held up as one of world leader in cybersecurity, with a super-connected society, and has built up it’s cyber-defence capabilities to world-leading levels in a matter of years following the attacks in 2007. Seen in this light – without the rhetoric of cyberwar and the with the reality of precedent – Scotland’s cybersecurity seems thoroughly achievable.
The cybersecurity debate is the military and security one in microcosm. The idea is that the problems are beyond the capacity of the layperson (the non-insider) to understand: the issues are too complex and too dangerous to consider a change of approach, and by extension, they should not be open to popular or democratic debate. This style of debate also tends to separate issues of security and defence from the rest of social and political life – with the result of making them “reserved issues”, not necessarily for the UK, but for a closed elite of insiders offering little in the way of accountability or real scrutiny. We’ve got a chance with independence to reset the relationships between security policy and politics – and to really make the former subordinate to the later. We’ve got the opportunity to get rid of they decaying model of UK defence and security, one of an oversized military and almost pathologically unaccountable intelligence culture. We shouldn’t need a large expeditionary military capacity because we’ll get the chance to gie dialogue and cooperation a try. We shouldn’t need a huge intelligence apparatus because transparency and proportionality can do the job in an accountable and effective way. Which is to say, more broadly, that we can move beyond a conception of security based on fear and paranoia, on an inherent elitism and social division, because when you look beyond the borders of the UK, you can see that it doesnae have to be like this.
———————————————————————————————————————————–